Modern companies operating in the information and communication technology (ICT) sector offer a wide range of services from providing communication channels and hosting client information resources to developing end-user applications and building large-scale systems serving billions of requests. ICT players actively rely on advanced IT solutions and business automation tools since their success directly depends on the technology.
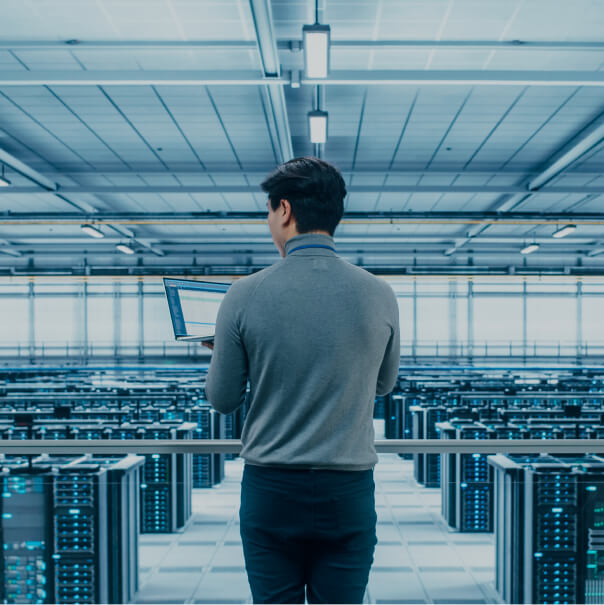
Remote work formats have been in place for more than 15 years in this sector, having become commonplace. A typical ICT company employs great numbers of IT professionals and information security (IS) specialists who are directly involved in customer services, including application development. This means that businesses in this sector tend to have a more sophisticated IT infrastructure compared to any other sector of the economy.
Yet, since ICT products exist and function as part of information systems, any system disruption or data breach may cause significant harm to both product developers and their customers.
This is why ICT players are some of the most popular targets of cyberattacks. Attackers may aim both at internal information resources and customer-facing components.