Robust information security implies using a number of organizational and technical measures to safeguard your information, as well as physically protect your data from various threats. Cyberattacks today may be targeted at more than one system, which means that you need comprehensive cybersecurity systems to mitigate them.
It is evident that a single protection tool, no matter how advanced and effective, cannot avert all applicable cyber threats. For example, even when you are using a comprehensive security system, it may still be vulnerable if your users have weak passwords that can be easily cracked, such as «123456». Even the most advanced tools designed for protecting your company’s information systems won’t make sense in this case since critical vulnerability lies at the very core of your security system.
On the other hand, it would be wrong to assume that all cyber threats are purely digital in nature and having comprehensive technical security would be enough to protect your corporate resources.
For example, strong user authentication is often used for remote sessions, while local access may still be protected with regular passwords. When additional authentication factors are used for connections to public resources, one often disregards the most important question: Why is this necessary in the first place? The purpose of strong authentication, as a remote access security tool, goes beyond preventing free use of passwords by attackers in the context of uncontrolled connections. The first reason why alternative authentication factors offering higher security levels, as well as additional methods to protect remote desktops and public resources, may be required lies in the fact that physical protection of information may be unattainable in certain situations (when you cannot introduce entrance checkpoints, use video surveillance, install lockable doors, safes, etc.).
At the same time, physical protection of information resources is just as important as the technological means used to safeguard your data. This is why physical access security and control require no less attention than the protection of logical access.
Both of these processes related to access security rely on the same subprocesses:
- User registration
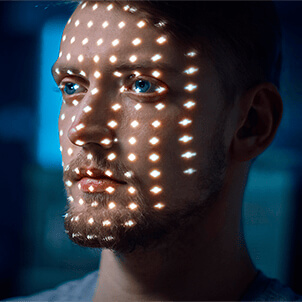
- User identification and authentication
- Controlled access of your access subjects (employees or users) to your access objects (premises or IT resources)
Given their similar structure, the two processes can work in concert and complement each other. For example, you may want your employees to be able to log in and connect to your corporate resources in the designated rooms only. This may sound too obvious, and this is why this arrangement may not get as much attention as it deserves. The fact that an insider who was able to steal a login and password of a legitimate user may try to log into the system from their workstation is often overlooked.
If your company uses simple password authentication coupled with geolocation, you can say that what you actually have is a full-scale two-factor authentication since two factors, password and geolocation, are required for gaining access to your resources. The room itself is also protected, with access available only to authorized employees. RFID cards designed for physical Access Monitoring and Control Systems (AMCS) are often used for this purpose.
In order to enable two-factor authentication (password and employee geolocation) at your company, you need to integrate your AMCS system with another access security and control solution intended for individual workstations. At the same time, this solution must support contactless RFID cards that can be used both for authorization at desktops located in protected spaces and for gaining access to other less critical workstations located in public areas (for example, terminals at production shops).