Identifiers and authenticators are the most essential elements for verifying user access rights. A potentially unlimited number of people may know your identifier, it often being the same as your email. On the other hand, authenticators are kept secret, thus becoming the most common target for cyberattacks. Intruders who were able to gain access to authentication data get an opportunity to secretly engage in malicious activity on behalf of legitimate users.
Most authentication systems still rely on passwords (secret words). This means that they remain vulnerable to password-cracking and social engineering techniques. Moreover, in case a password is stolen, you are not likely to be able to detect this until an explicit security breach has occurred.
Specialized strong authentication technology based on relevant software and devices (tokens, smart cards, one-time password generators, smartphone apps, etc.) should be sufficient to counter the threats and issues related to password-based authentication.
These IT solutions can counter most threats associated with identification and authentication systems. Yet, we should always keep in mind that for criminals, the bottom line is their potential financial gains. Whenever large amounts of money are at stake, intruders will stop at nothing to try and gain access to critical data (trade secrets, financial statements, control consoles for critical processes, etc.). They may even come up with criminal schemes to obtain passwordless authenticators by stealing hardware tokens, compromising certificate authorities that issue certificates, etc.
The data and IT infrastructure segments that may have high value in the eyes of intruders require the most effective information protection technology.
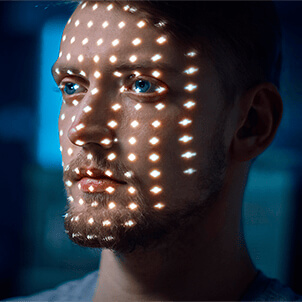
Biometric systems are the best tools for ensuring effective strong authentication at a top security level. Their key advantages over password-based systems and other solutions relying on hardware tokens or digital certificates are listed below.
- Your authenticators cannot be compromised since it is impossible to steal or publish the physiological and behavioral characteristics of your employees. Modern biometric systems are highly accurate and can detect most attempts to use a fake biometric authenticator.
- The risk that your authenticators may get damaged is quite low since users are most likely to treat their own body with more care compared to any hardware token
- Users no longer need to remember secret information or carry a special device. A person’s biometric characteristics are an inherent part of them, so they are always at hand.
In other words, when biometric authentication is used for protecting confidential information, access to such information will require the physical presence of a given user.
Successful deployment of a biometric authentication system calls for its integration with existing corporate services and applications.
The optimal solution would be to use biometric scanners in combination with the Two-Factor Authentication (2FA) Provider and Enterprise Single Sign-On (ESSO) solutions. This software suite will provide you with an authentication system that cannot be bypassed and supports biometric authentication across all corporate services and applications.