Centralized access management systems have distinctive features that set them apart from the centralized control systems designed for other information security tasks. For example, in case of perimeter defense, all you need to do is buy a hardware and software unit from a single vendor and then use a single console for process management and monitoring. The same is true for other processes related to information security, such as protection against cyberattacks and viruses, or leak detection. For all these processes, there are standalone solutions with central management features.
So, in many cases you can purchase and use specialized technology solutions for various information security tasks, but when it comes to access management, you are most likely to already have a few elements in your IT infrastructure, as you may use isolated authorization systems for each individual service, desktop or web application, and operating system.
Not only are these systems self-sufficient in terms of identification, authentication, and access control procedures, but they may also have their own management consoles and event logs.
In this case, you may have to deal with a high level of fragmentation in terms of monitoring and management of user accounts, which makes it difficult to apply a uniform access management approach. Likewise, each service or system may have its own name notation and keep a log of its own information security events. This can make the investigation of access-related incidents rather challenging, especially if you do not use a Security Information and Event Management (SIEM) system.
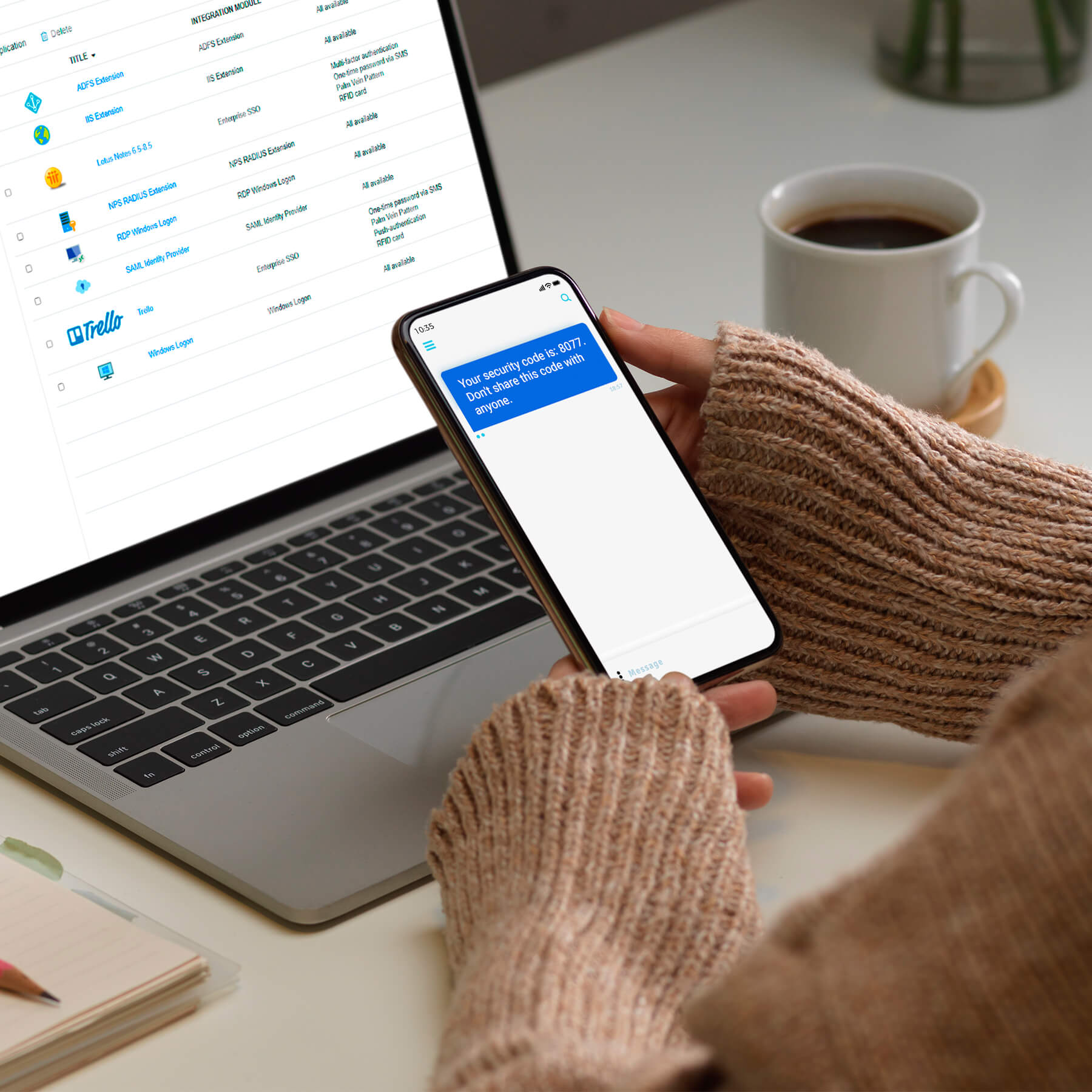
If uniform access policies cannot be applied, this means that no uniform policies are in place for managing all the authenticators, including passwords. If your company relies on several services with isolated authorization systems, you may find yourself in a situation when your users are forced to use several authenticators (passwords).
One way to introduce centralized access and user account management in your company is by purchasing an Identity Governance & Administration (IGA) solution. However, the deployment of such solutions may prove extremely difficult, let alone the fact that some of them may not include authentication management modules or lack support for various strong authentication scenarios. The main purpose of IGA systems is to help you manage the lifecycle of your user accounts and related permissions across all target systems, devices, services, applications, and web applications.
Various issues that have to do with proper operation and administration of isolated authorization systems may cost your company time and money, as well as make it vulnerable to cyber threats. In this case, the optimal solution would be to use a specialized Access Management product designed for access security and control.