Most governmental and commercial organizations today (except for classified facilities) have set out on the road to remote work. Both individual employees and entire departments may be offered to transition to telecommuting.
There are two main remote options depending on duration:
- Temporary arrangements when your employees or departments need to work remotely due to short-lived objective reasons, such as business trips, illness, and other situations.
- Permanent arrangements when telecommuting is the only option available to employees.
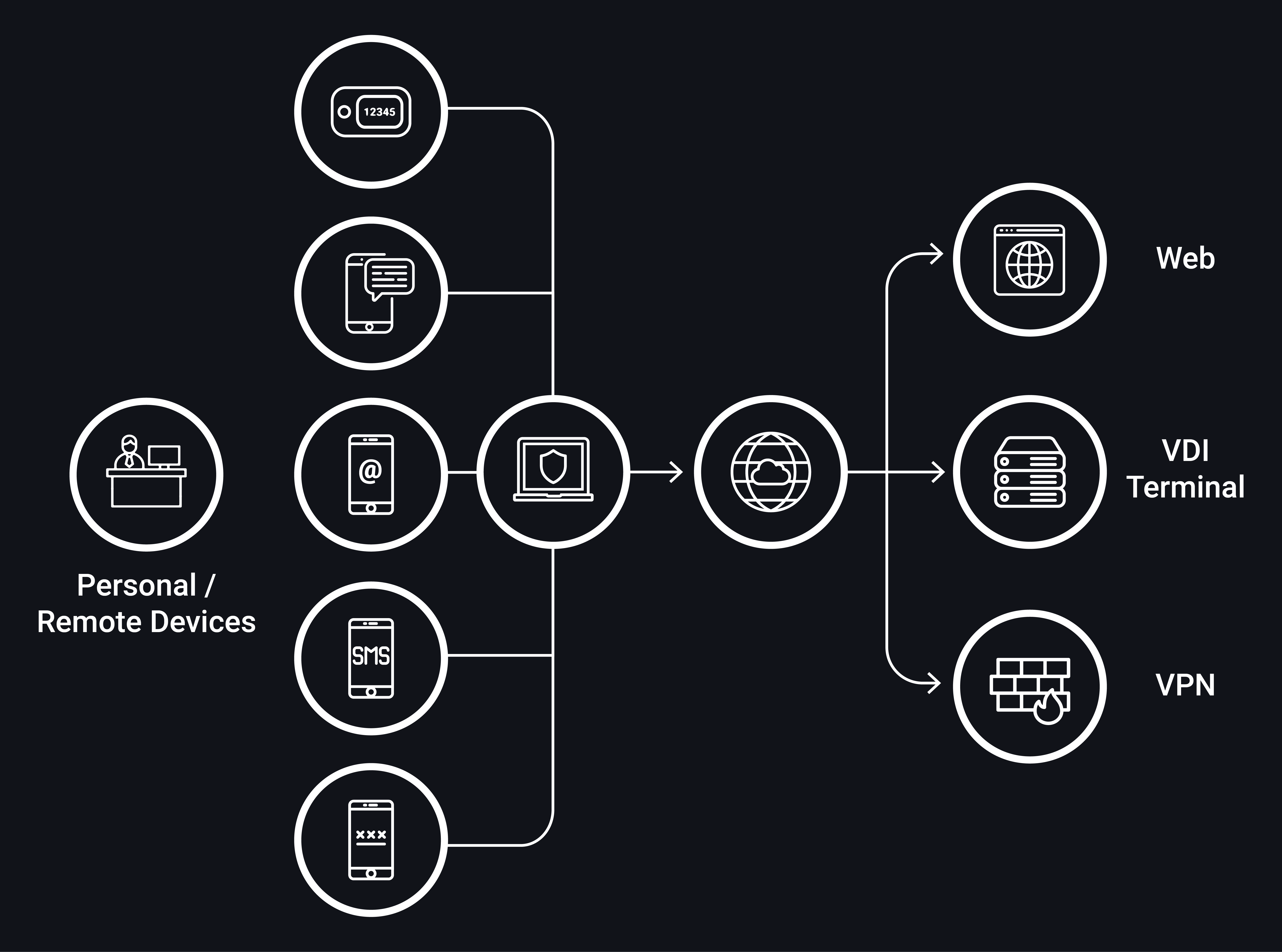
One of the most important parts in telecommuting is to ensure remote access to corporate resources. The following remote access resources can be used in this case:
- Corporate web resources
- Application servers (terminal servers)
- RDP server
- VPN gateways
- Virtual desktop infrastructure (VDI server)
It is important to keep in mind that some technical, organizational, and physical means designed to protect information cannot be used in telecommuting. For example, physical protection of a remote desktop is simply unachievable, while the use of technical means to protect information at the level of network perimeter may prove quite challenging. This is why the bottom line of remote access security is adequate protection of your employees’ desktops as well as corporate resources used for your employee connections.
The main sources of cyber security risks in the context of telecommuting are as follows:
- Low security of personal devices of your remote employees
- Low security of network environment at your employees’ workstations (irrespective of whether they use a personal device or a corporate solution)
- Uncontrolled connections to resources via smartphones and tablets
- Direct web access from workstations used for critical processes
- Situations when it is impossible or very hard to apply corporate network security solutions (including anomaly detection)
- External access to critical corporate resources
- Tight schedule of changes in your network architecture to ensure prompt access to work resources while threat modeling is often overlooked
- Excessive permissions granted to employees
All IT resources (access objects) are designed to grant access to named access subjects (users). This is why one of the key tasks of information security systems lies in preventing the illegal use of employee credentials for all attempts to connect to corporate services (i.e., credentials theft). This makes secure authentication a prerequisite for all remote sessions.
The best way to ensure remote access protection is to use hardware and software that offers unified strong authentication scenarios for all attempts to connect to the resources accessible from the outside. This comprehensive solution must include specialized software and hardware enabling strong authentication, as well as a Two-Factor Authentication (2FA) Provider, another solution that supports strong authentication across various corporate resources.