Real-time monitoring
The Axidian Privilege platform enables real-time monitoring of administrative activity. It
supports simultaneous scaling and monitoring of multiple administrators.
PAM functionality will allow you to view all active sessions from your admin console.
Should a PAM administrator notice any suspicious or precarious activity, he/she can
manually terminate the session and suspend access for a given privileged user until
the situation is resolved.
Real-time monitoring can be very useful when your users need to have remote access to
critical resources and systems. If you use the Axidian Privilege system, you will no longer
need to cover the travel expenses of your remote privileged users, so that they can
visit your location, and you can oversee their work. Your remote employees can
connect to a critical resource at any time whenever this is required, and all their
activity will be recorded.
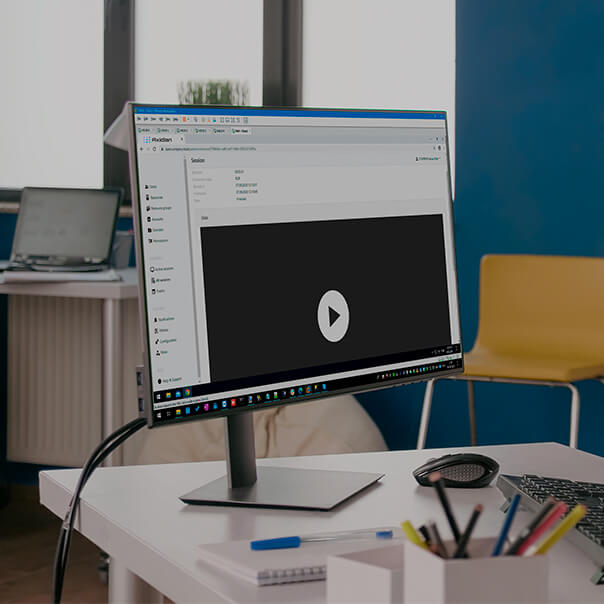
Session log
If you use the Axidian Privilege single centralized vault to keep your privileged session
data, you will no longer have any issues with obtaining detailed incident
information from a corrupted resource. All privileged user activity for those users
who were placed under control will be fixed in the event log.
Another important feature of Axidian Privilege is the two-factor authentication option. On
the one hand, 2FA will guarantee an additional level of security for your remote
connections, and, on the other hand, it will make it almost impossible for
privileged users to play victim in the event of malicious activity from their
accounts.
You can get information about all administrator sessions, including access time,
duration, username, and target resource. The Axidian Privilege log includes a tool enabling
session search by specific criteria.
By using these features, you can not only find the cause of almost any situation, but
also use session logs for other purposes: for example, for monitoring working hours
and analyzing errors, which can be essential for your new employees.
Video records and text logs
The Axidian Privilege platform can record all privileged user activity as video files and
text logs.
Privileged user activity can cause a system failure, impairment in the performance of
your target resource, or disruptions in the work of a corporate application.
Sometimes, there is no exact match between the declared and factual quality of work
done by privileged users. And, in many cases, the factual quality can be worse than
you expected.
The Employee Monitoring Products and Services (EMPS) designed to assess the
performance of your employees during business hours and record their activity have
significant limitations in terms of privileged user monitoring, including the
following:
- Privileged users can disable or remove an EMPS agent from their workstation or
server.
- Target resources may not support installation of additional software (this is
especially true for devices).
- A privileged user can work for another organization (being your contractor) or
use a personal device to access the target resource, in which case you will not
be able to install an EMPS agent.
If you use Axidian Privilege and have an emergency or need to perform in-depth analysis of
privileged user activity, you can download all relevant logs and pass them on to
your responsible personnel so that they can make relevant decisions and
organizational conclusions.
File transfer control
The PAM system can detect file transfer and create shadow copies of files in the PAM
database. This may be essential when a user needs to send or download a specific file or
document to/from a server during an administrator session.
In this case, file transfer is normally made via standard administrative protocols. RDP
permits remote connection of a logical disk to the target system during a terminal session.
For example, you can upload updates on the server or, vice versa, download reports or
configuration files from the server.
PAM functionality designed to detect file transfer and create shadow copies of transmitted
files can help you understand what kind of information was transmitted and whether or not
critical data was involved.
Overriding commands and managing user privileges
The Axidian Privilege platform can monitor the commands entered during an administrator session
In some cases, it is hard to predict which activity may cause a target resource failure or
disrupt proper operation of a business service. In other cases, certain activity may have
delayed effects and cause system failure or incompatibility in the future. For example, it
can be the launch of software or operating system updates on the server.
The PAM system response to detected malicious commands includes two steps:
- The user session will be terminated to prevent command execution and related failure.
- A responsible administrator or resource owner will be notified about the event.
The system offers two options for filtering the commands:
- Forbidden Command List — «anything that is not expressly forbidden is allowed».
- Permitted Command List — «anything that is not expressly allowed is forbidden».
The second option will allow you to manage privileged user rights by setting a pre-defined
list of permitted actions.
User notifications and integration with monitoring systems
The PAM system allows sending notifications about critical or important events to responsible
officials, including administrators, top managers, and users. All notifications will be sent
to the SMTP server. You can customize the list of events when relevant notifications should
be sent.
The Axidian Privilege platform supports integration with the Security Information and Event
Management (SIEM) products; the event data will be transmitted via the syslog protocol.
SIEM integration will allow, for example, setting up rules for event processing and
correlation. And these rules can help detect connections to critical resources that
circumvent the PAM system (when an event gets registered by the resource, but does not get
registered by the PAM platform). In case of failure or breakdown of a resource, SIEM will
show the list of employees who had access at the time of the failure, even if the resource
did not have enough time to send logs to the SIEM system.
Incident investigation
Analytics and source metadata may not be enough when you investigate information security
incidents related to privileged user activity. You may require more information to establish
the true cause of a system failure, get the incident under control as soon as possible, and
take measures to prevent its occurrence in the future. The lack of data may also require a
lengthy investigation and reduce its overall quality.
When you have the Axidian Privilege system at your disposal, your investigation will include the
following steps:
- A privileged access incident is detected.
- A selection of incident-related administrator session records is prepared.
- Session records are examined and analyzed.
- The complete sequence of events is reconstructed (including the series of actions that
have caused the failure).
- The identified dangerous sequence of actions is fixed in a corresponding document, or
adjustments are made in the user instructions.
- Relevant measures are taken to restore the operational condition of the resource.
- Relevant measures are taken against the person responsible for the incident.
By using this functionality, you can significantly reduce your incident response time, which
will not only improve the productivity of your personnel, but also save resources for your
company.
Ungrounded accusations
After a critical resource failure, you may find yourself in a situation where an innocent
employee has to face ungrounded accusations because of indirect incident markers pointing in
his/her direction (he/she had access to the resource at the estimated incident time). In
this case, your company may lose a specialist with high potential and worsen the working
environment in your team.
If you are using the Axidian Privilege system, you will have conclusive evidence to identify the
person responsible for the system failure and establish the degree of their malicious intent
by analyzing relevant activity logs (video records, text logs, command lists, transmitted
files, connection time, protocol/application, etc.).
In this case, honest and trustworthy employees have nothing to fear — even if they were
responsible for the incident but did not have malicious intent (anyone can make an error),
they can rest assured that they will get an impartial assessment of their actions.