There is currently much controversy over the PKI status in modern cybersecurity which raises a number of curious questions. What is the PKI role in digital transformation? When does the new era of cryptography start? We have collected these and other exciting and hot-topic questions about PKI now and future and addressed them to Nevenko Bartolinčić, Senior Security Architect of Span and PKI expert at the roundtable «Evolution of Trust: Get ready for PKI 2.0»
What do you think is better: centralized or decentralized PKI?
PKI is by design centralized, Certificate Authority (CA) guarantees ownership of the particular public key. For that reason, it is limited what we can do, and we have to live with some restrictions. Certificate owner really does not own certificate, CA can revoke it at any moment, certificate verification reveals the history of user interactions.
If PKI is under one administration authority, then the decision of how many levels of hierarchy and how many root servers to use depends on the customer environment and needs. Factors to consider are: how many certificates must be issued by CA, do we need to issue many certificates with identical names, is it important to secure certificate verification to protect the history of user interactions, do we need to avoid the central point of failure, do we need separate policies, do we need to take care of some compatibility issues.
If there are multiple administration authorities than we can consider bridge CA.
The truly decentralized solutions are of limited use; PGP for scalability limitation, Blockchain for immaturity reason.
Can PKI resist the post-quantum threat?
Yes, it can survive. Quantum computing will make useless current public key algorithms such as RSA digital signature and Diffie-Hellman Key Agreement. This technology is used everywhere, not only in PKI, and it will impact many areas including critical infrastructure, IoT, TLS/SSL, IPSEC, SSH.
My expectation is standard organizations will come on time with new algorithms as other solutions are complicated for migration.
It is hard to forecast how much time we have, but the predictable start of the new cryptography era is between 2023 and 2030. Many current Root CA are valid well beyond that date. Everything that must be protected over a period longer than 10 years is threatened. Anything signed now will not have integrity in the post-quantum era.
What can we do now?
a) Closely watch what standard bodies (e.g., NIST) are recommending on quantum cryptography.
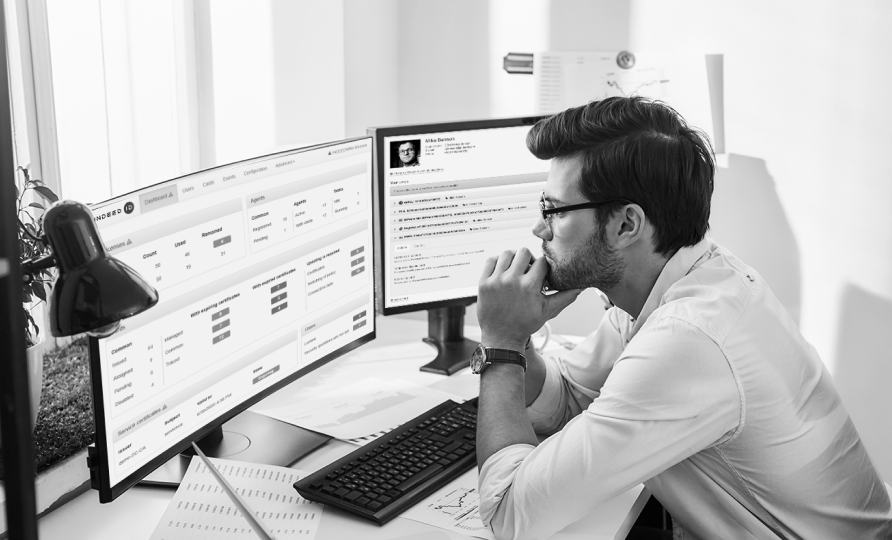
b) Prepare current PKI processes for an easy and fast transition to new technology; have an inventory of keys, what for we are using them and automate their management.
c) We cannot continue to rely only on cryptography, whenever possible we should implement additional security controls.
Can PKI and audit requirements go hand in hand?
Yes. But it depends on what audit you have in mind. PKI can help in fulfilling compliance requirements and passing audit as it guarantees the identity of a user and provides nonrepudiation. The activity of PKI as a tool can be easily audited as all available PKI tools provide a good audit trail. Auditing operation of PKI as Certificate Authority can be very complex and expensive since those requirements are sometimes very strictly regulated, particularly in CA is issuing the qualified digital certificate.
PKI in the new normal of remote work. What development and opportunities will remote work bring to PKI?
I have seen many talks and presentations about digital transformation. Most of them were just empty words, but COVID-19 changed everything like in the following joke.

A simple test of company digital transformation is: can all work from home? Do, not forget management and finance.
Remote work does not only complicate usual communication, it also makes some usual business processes impossible, particular if they rely on paper and physical contact. This opens a lot of opportunities for PKI, nothing new, just refocus due to the inability to work in an old way. I will give just a few examples: strong smartcard authentication of users, SSO for applications, VPN authentication, mail signature, signing PDF documents. This enables easy user provisioning, comfort work and audit trail of business activities. The bonus is that documents are easier to find and that all have a digital trail.
We invite you to discover more experts’ insights on the existing PKI trends and dip into PKI 2.0. Request the roundtable recording and stay tuned with the PKI evolution.