Management of risks – both reputation and financial – is one of the most important business tasks. Confidential information and internal regulations of any company is a higher priority target of business intelligence and competition. Protection of such data is a matter of confidence and high responsibility. Therefore, not all users of business information systems have privileged accounts.
However, the presence of privileged users proper does not guarantee protection from data leakage or illegal actions of employees or other interested individuals. Information security stipulates for not only regulation of access to important data, but also an audit of user actions.
The basis of Axidian Privilege (Axidian Privilege) is the system of controlling the privileged user actions. The said system provides for solution of the following tasks:
- provision of screen recording (video recording of privileged user actions on a computer);
- provision for session text recording (record of all launched processes and keyboard input);
- storage of user action records in archive with indication of user account and server where the action took place (including RDP sessions).
Control of privileged user actions cannot be provided for via information system administrator account only. For this, you need a fully functional system with an opportunity to track all the operations performed. It can be implemented, for example, via event log and recording of privileged sessions.
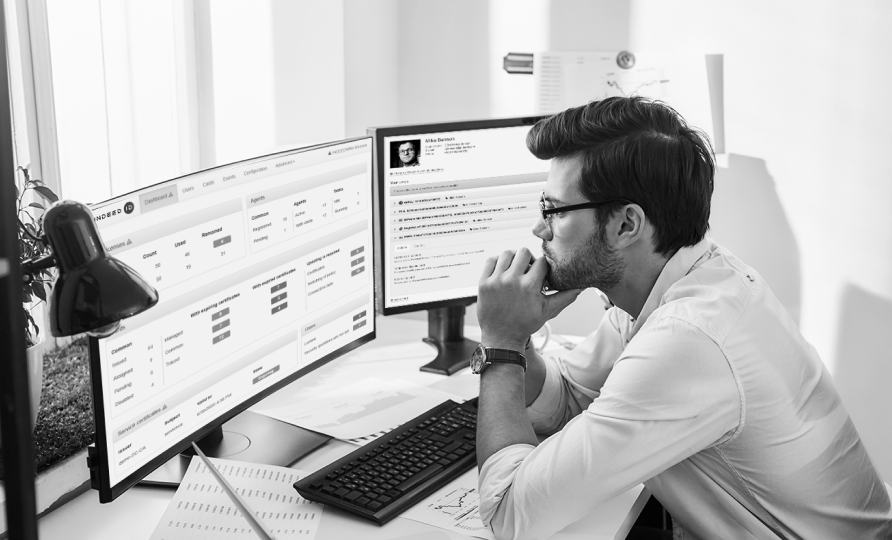
Session recorder module of Axidian Privilege makes it possible to track who used privileged access, how and what for. This is possible due to that the Axidian Privilege is a web application working on Internet Information Services (IIS) server. Therefore, you can set up access parameters either locally or remotely.
The administrator console allows for general management of access to critical data for an employee (access level, accounts) and user action audit.
Audit is possible due to that the Axidian Privilege provides for recording and storage of employee sessions of all types (RDP, SSH) as text, video and screenshots. Only complete system of controlling the user actions allows the business owners to find out what privileged accounts are used for by employees and how. This, in turn, provides for internal protection from reputation and financial risks for the company. For more details about Axidian Privilege operation please visit our website.