The Axidian Privilege software suite has been updated to Version 2.6. The release includes a lot of improvements and a number of new features that make activity log […]


The Axidian Privilege software suite has been updated to Version 2.6. The release includes a lot of improvements and a number of new features that make activity log […]

For most companies PAM is something that is associated with creating borders or limitations. Often organizations are forced to implement PAM due to the legal regulations and do […]

Our EMEA Director, Konstantin Krasovskij presented on the Expert Stage at EIC2021. Konstantin discussed the importance of building a new mindset on PAM implementation and gave some tips […]

The growing importance of implementing privileged access management at the corporate level is noted by leading cybersecurity analytics. They mention that “by 2024, organizations that use privileged task […]
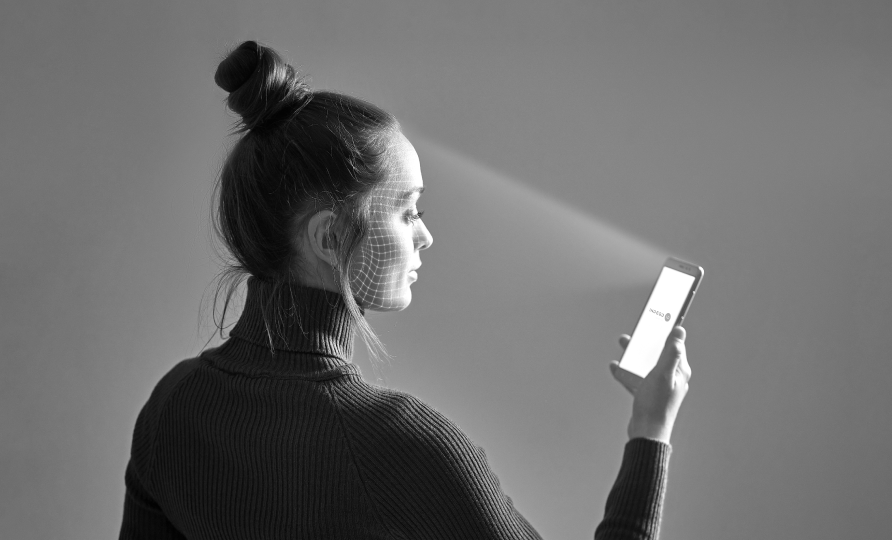
When it comes to multi-factor authentication, any cybersecurity officer knows – usability is a must step toward users’ acceptance of the technology. The product will be ignored if […]

Ensuring the highest level of security, Public Key Infrastructure enables core enterprise processes of users’ authentication, encryption and digital signature. Just like any technology, PKI actively evolves and […]
Smart cards have been a part of the information security market for several decades already and are used by companies for the identification of employees. The evolution of […]
There is currently much controversy over the PKI status in modern cybersecurity which raises a number of curious questions. What is the PKI role in digital transformation? When […]
The roundtable «Evolution of Trust: Get ready for PKI 2.0» was about the most confusing, yet vital topics that remain puzzles to many cybersecurity experts. Has COVID-19 affected […]

In the digital era, PKI is one of the most effective technologies for authentication of users and devices that is used by worldwide companies for decades already. However, […]